 Hackers continue to refine their intrusion techniques to create more sophisticated attacks. But they still use tried and true methods. One is a brute force attack, a trial-and-error hacking method to crack passwords, login credentials, and encryption keys. They systematically try or steal, different usernames and passwords until they log into the system correctly.
Hackers continue to refine their intrusion techniques to create more sophisticated attacks. But they still use tried and true methods. One is a brute force attack, a trial-and-error hacking method to crack passwords, login credentials, and encryption keys. They systematically try or steal, different usernames and passwords until they log into the system correctly.
Because it takes the mere skill of deduction, brute force attacks remain popular for hackers as an aggressive tactic to force access to user accounts. We will dive into the different prevention tools your company can implement to thwart brute force attacks.
What are the different types of brute force attacks?
Due to its popularity, the brute force attack has a Swiss army knife of methods hackers can use when barging through your login portals.
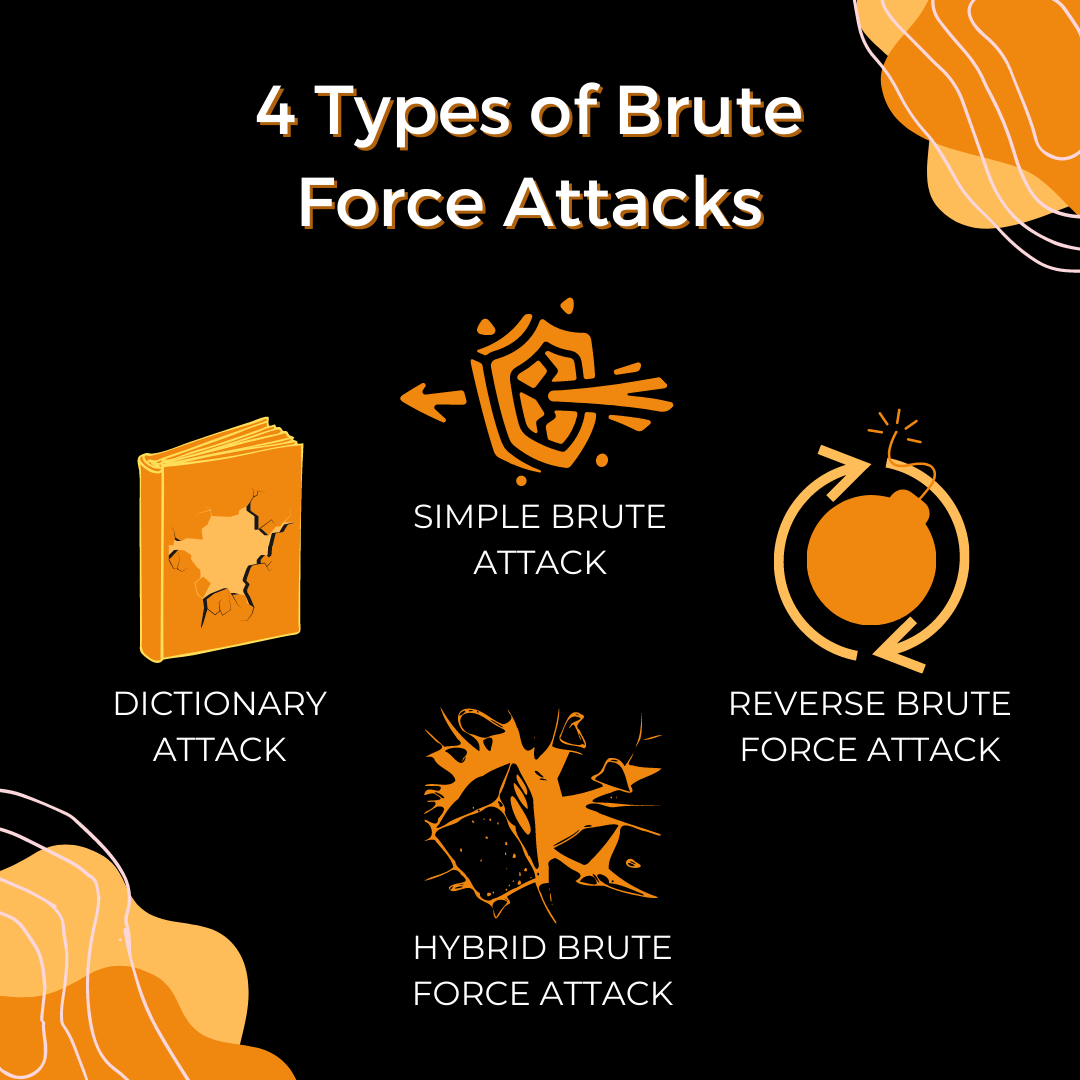
Simple brute force attack
Like the name, the simple brute force attack is when hackers attempt to guess a user’s login credentials without using any software. They will manually enter standard password combinations or personal identification number (PIN) codes until they think of the correct one.
Simple brute force attacks guess weak passwords, such as “password” or “123456.” They will also research basic information you or your employees post online to answer security questions, such as the name of your favorite sports team, maiden name, or your hometown.
Dictionary attack
A dictionary attack is a brute force attack in which the hacker selects a target and tests a possible password against the individual’s username. Dictionary attacks are more time-consuming, as hackers make multiple attempts by switching out special characters and numbers within a passphrase. The chances of success are unlikely but play an essential role in helping the hacker figure out login credentials.
Hybrid brute force attack
Hackers will combine the simple brute force attack and the dictionary attack to double the brute force power. The hacker will take the username and begin guessing a list of potential passwords. Then they will experiment with different characters, letters, and number combinations until they run through the list or are successful. Some examples include “Br0nc0s2021” or “Hu$k3r$1969.” While this is also time-consuming, the potential payday in store for them is worth it.
Reverse brute force attack
Brother to the dictionary attack, the reverse brute force attack takes a valid password to search for a matching login credential through a list of usernames. Hackers may also try common passwords, such as “password123,” then search millions of usernames until they find a match. Many hackers discover leaked passwords that are available online.
Credential stuffing
Credential stuffing is a continuation of the previous techniques where the hacker collects username and password combinations they have obtained and tests them in other login portals to see if they can gain access. Suppose you or your employees reuse usernames and passwords for emails, social media profiles, or business accounts, this is an easy way for hackers to blast through security measures and break into your system.
Brute force attack tools
Because the guess-and-check system can take hours of a hacker’s time, they have developed tools to make the process go faster. These include:
- Tools that examine Wi-Fi network security to monitor and export data while also attacking your business through weak access points.
- John the Ripper- a password recovery tool that supports hundreds of cipher and hash types for different technologies, accounts, and applications to find hidden sensitive data.
- Automated tools guess usernames and passwords at a rapid speed, inserting every possible password to see if it works.
How can my business fight against brute force attacks?
You can apply multiple solutions throughout your business to prevent hackers from breaking in.
- Build strong password habits.
- Create passwords that are longer than 12 characters
- Include numbers, uppercase, and punctuation characters to make the password more unique
- Do not use dates (such as birthdays or anniversaries), addresses, or phone numbers as your password
- Do not force complexity- try to keep it simple, but original to who you are as a person
- Avoid recycling passwords
- Use a password manager
You reuse passwords because they are easy to remember and keep you from writing them down for someone to see. We get it. But reusing passwords increases the risk of hackers breaking into multiple accounts. Password managers make it effortless to create safe and unique passwords to use while automatically saving them in the password vault where only you can access them.
Whether it is a code sent to your email, push-based, or a text message to your phone, MFA adds another layer of security to prevent a break-in. If a hacker does manage to find your login information you are notified of the hacker's attempt to sign in. As a result, you then are able to deny access and/or shut down your systems before the hacker can get their hands on any data.
- Provide password training for your staff
Not just when they are onboarding, either. Consistently communicate your updated password protection policy and what proper implementation looks like, so your employees can apply them throughout their workday. CoreTech will implement an easy and educational training program that teaches your employees the latest threats, and how your staff can reinforce defense practices to protect your business.
- Limit the number of login attempts
Hackers will try to log into your accounts hundreds of times rapidly. By limiting the number of login attempts, your system will lockdown, and the hacker will not be able to try again- stopping them in their tracks. Even a temporary lockout will delay a hacker from figuring out your credentials. As a result, hackers move on to more accessible passwords that take less time to crack.
Put a padlock on your passwords
The CoreTech team can help your company and staff implement the security tools above. In addition to a security training program, we’ve written a FREE guide on all you need to know about password management. Let us help you lock down your systems and keep the hackers out.

