.png?width=350&height=215&name=CEO%20and%20Cybersecurity%20Blog%20Post%20(1).png) A 2023 report by Cybersecurity Ventures predicts that midsize businesses spend about $826 to $653,587 on cybersecurity incidents. It further asserts that the costs of cyber crimes will reach an estimated $10.5 trillion by 2025. The constant increase in the cost of cyber attacks in business is a message for Chief Financial Officers to take adequate threat-detection measures so that their organization doesn't become victim to a security incident.
A 2023 report by Cybersecurity Ventures predicts that midsize businesses spend about $826 to $653,587 on cybersecurity incidents. It further asserts that the costs of cyber crimes will reach an estimated $10.5 trillion by 2025. The constant increase in the cost of cyber attacks in business is a message for Chief Financial Officers to take adequate threat-detection measures so that their organization doesn't become victim to a security incident.
If those figures are not enough to motivate midsize business decision-makers, the World Economic Forum revealed another interesting aspect of enterprise security: about 95% of cybersecurity issues occur due to human error. The growing costs of cyber attacks make it crucial for users to be trained to prevent attacks using the latest preventative technology tools, employee awareness, and cyber security training.
If you are a CFO investigating how to enhance cybersecurity for your business, below are some key concepts you will want to be aware of, including what common vulnerabilities, threats, and exploits are. To secure your organization, you must have clarity on how attacks occur and where you need to protect yourself. Though many people confuse these terms and sometimes wrongly use them interchangeably, there are distinguished differences between them, and knowing that distinction forms the basis of any safeguards you employ towards each of them.
What Is a Vulnerability?
A vulnerability refers to a weakness in the information system (e.g., application, operating system, or network) that allows threat agents unauthorized access to confidential information. It is a security vulnerability that allows adversaries to exploit systems and networks, for example, system misconfiguration or software code flaws.
A 'bug' in the application can give attackers access to confidential files. Then, the application provider releases a security patch to fix the issue at the time they discover it. However, if you do not update patches on a timely basis, you are still vulnerable to that security flaw, and a malicious actor can easily reach your internal network. Routine vulnerability testing and efficient vulnerability management are crucial factors for ensuring cybersecurity.
What Is an Exploit?
If a vulnerability is a security flaw, then an exploit is the means designed to take advantage of that vulnerability and target an asset (e.g., a malicious software program). Usually, exploits are designed to gain administrative control of assets. For instance, the exploit of a database vulnerability allows attackers to gain access to and steal database records.
What Is a Threat?
A vulnerability is a known system flaw, and an exploit is a vector to leverage that vulnerability. A threat is imminent ‘danger.’ A cyber threat is a malicious or harmful act aimed at compromising your digital data, stealing it, or deleting it. Some threat examples include viruses, data leaks, and attacks that slow down your systems.
For example, an employee using weak passwords to protect confidential organizational data is a vulnerability. An attacker who devises an email phishing scam where he attempts to impersonate a superior and ask the target employee to share sensitive information assets is the 'exploit' strategy. And the phishing scam itself is a ‘threat.’
How Do Vulnerabilities, Exploits, and Threats Impact My Business?
To answer that question, you must first understand the common attack vectors that cyber adversaries use to target organizations and individuals. Phishing and ransomware have remained the most effective attack vectors in the last decade, and they continue to lure users with clickbait and demand hefty ransoms after encrypting data in a network system. Vectors like DDoS (Distributed Denial of Service) attacks, Advanced Persistent Threats (APT), etc., are other threat factors you must establish security controls to guard against.
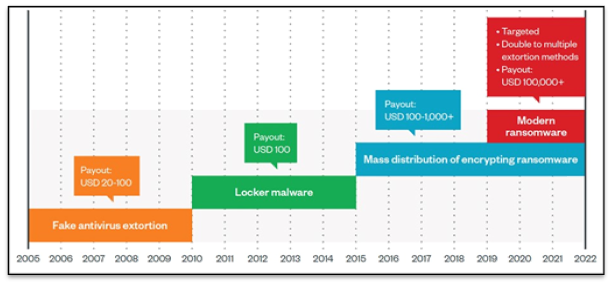
(Source: Trend Micro)
The graph above by Trend Micro shows the trajectory of ransomware attacks and the changing patterns and costs of these attacks over the past 17 years. Beginning with fake virus threats, they transitioned to Locker malware and the current era of customized double and triple extortion campaigns. The attackers aim to gain financially from the businesses they target, their employees, affected clients, and customers. Then they also gain by selling stolen data.
A knowledgeable Managed Security Service Provider (MSSP) will help you mitigate risks and prevent emerging threat factors. Before finalizing a relationship with an MSSP, you must educate yourself on the investment you are making in security and why. Here's what cyber attacks could cost your business.
Direct costs
Several direct or immediate expenses accompany a cyberattack. While businesses that are prepared and have recovery plans in place have an easier recovery journey, midsize businesses often find it highly difficult to overcome the direct costs of a cyber attack. Some of these include:
- Intellectual property: Loss of valuable information assets or confidential business files, including business secrets and patent information, is one of the most significant expenses to an organization.
- Financial losses: Downtime, disruption in business flow, and peripheral losses involving reputational damage drain an organization significantly.
- Regulatory fines: Failing to update security patches, inform affected clients, etc., can invite unwelcome penalties from regulatory bodies and law enforcement.
- Incident investigation and recovery costs: The post-attack investigations and system reinstallation processes often involve hiring field experts, which can be expensive.
- Customer compensation: A breach involving the compromise of customer data compels organizations to offer heavy compensation for them, which is a substantial financial burden.
Indirect costs
A cyber attack can also result in indirect losses with a long-term impact, including monetary and non-monetary costs. Some of these are:
- Customer trust: A cyberattack might cause your customers to lose faith in your privacy and security measures. Consequently, they switch to alternative brands or organizations offering similar services.
- Loss of goodwill: The brand name you and your employees take years to build can easily get tarnished with a cyber attack.
- Loss of prospective customers: Bad publicity from cyber-attacks could also manifest in a failure to attract new customers or convert existing leads.
- Risk of legal action: If customer data is lost in a data breach, then there is also the risk of customers taking legal action against your establishment.
- Downtime and decreased productivity: The time taken to recover from an attack translates to lost time, money, and staff productivity during those business hours.
How Do I Protect My Business?
Now that you understand the significance of protecting your business, you can now look at some proactive strategies:
- Security awareness: Investing resources to regularly educate your employees on cybersecurity basics and attack prevention methods is highly recommended. The training needs to Include mock phishing attacks to gauge employees' attack preparedness.
- Patch management: A robust patch management process to ensure timely patch updates is vital to enterprise security.
- Password management: Using multi-factor authentication and password management applications is helpful in attack prevention to a significant extent.
- Principle of least privilege: Ensure that offboarded employees' access to files is removed immediately and system access remains with only those who need it is a best practice for enhanced security.
- Advanced tools: Cutting-edge cybersecurity tools and solutions like Security Information Event Management (SIEM), dark web monitoring, and advanced firewall protection can go a long way in protecting your crucial data assets.
Exploiting vulnerabilities that use malicious techniques to gain admin access lead to the compromise of crucial information assets. Exploited vulnerabilities bring an array of challenges for a business, including financial losses and negative publicity. Therefore, organizations must prevent cyberattacks by identifying threats, fixing vulnerabilities, and leaving no room for security exploits.
CFOs may not have the time or expertise for cybersecurity management; they are focused on core business activities. That’s where CoreTech comes in. As an expert managed security service provider offering comprehensive security services, we are here to help! Contact us today.
Additional Resources
- Reducing Cybersecurity Risk in Your Business: CEO’s Leading the Way
- 4 Elements of an Effective Cybersecurity Awareness Training Program
- 8 Topics Your Employee Cyber Security Training Needs to Cover

