 The sole objective of any phishing email is to trick you into clicking a malicious link. If you aren't vigilant, phishing scams can be easy to fall for. It doesn't matter who you are, how much money you have, or what company you work for, you can be targeted and it's important to know how to protect yourself.
The sole objective of any phishing email is to trick you into clicking a malicious link. If you aren't vigilant, phishing scams can be easy to fall for. It doesn't matter who you are, how much money you have, or what company you work for, you can be targeted and it's important to know how to protect yourself.
Since Amazon and Uber are so well-known and widely used services, cybercriminals have often chosen them to impersonate. Their aim? To lull you into a false sense of security at receiving an email from a familiar brand name. With the addition of a subject line that will illicit a sense of urgency and a response, anyone could find themselves clicking on a link before even taking a second to think.
Amazon Phishing Emails
If you log into your email account and see this email, would you click one of the links?
.jpg?width=584&name=Phishing-Emails-(2).jpg)
A lot of people would click the malicious link, without a second thought, because they want their package. Or maybe they don't even remember ordering anything, but their curiosity gets the better of them. Or they think fraudulent activity has occurred on their account and they're just trying to be cautious.
These are the types of automatic responses cybercriminals prey on. But, if you take the time to look over this email before clicking, you will find some flaws and save yourself from turning over sensitive information or being the victim of a malware attack.
How can we tell that this email isn't really from Amazon? Consider the following red flags.
.jpg?width=584&name=Phishing-Emails-(2).jpg)
1. Look at the email address. It comes from notifications@amazin-delivery.com. A real Amazon email address is going to end in amazon.com.
2. You should always be wary of subject lines like these, where it's obvious they're trying to illicit a quick response. It's always important to take a minute to look over an email and avoid clicking links or opening attachments until you know it is legitimate.
3. If I have ordered something from Amazon, they definitely have my name and it's weird that they would address me by my email address.
4, 5, & 6. Always hover your cursor over hyperlinks before clicking on them. Anyone can make the front-end text say whatever they want it to say, but if you hover over the link, you can see where the url leads. Because I have Proofpoint Email Protection on my computer, every url that comes through my email starts with "https://urldefense.proofpoint.com/v2/url?u=" then it shows whether the url starts with "http" or "https" then it always says "-3a_" before showing the rest of the url. In this case, the url is "http://employeeportal.net-2dlogin.com." Since that web address has nothing to do with Amazon.com or even tracking a package, we know not to click on it.
.jpg?width=584&name=Phishing-Emails-(2).jpg) Most cybercriminals aren't going to use such obviously fake urls. Many end-users have been tricked by phishing emails created by cybercriminals posing as Amazon but instead of using amazon.com they used arnazon.com. When the users glanced at the url, they saw an "m" instead of an "r" and an "n." In other instances you could get a malicious email sent to you from someone you know. If their email account has been hacked, it could be incredibly difficult to identify a phishing email.
Most cybercriminals aren't going to use such obviously fake urls. Many end-users have been tricked by phishing emails created by cybercriminals posing as Amazon but instead of using amazon.com they used arnazon.com. When the users glanced at the url, they saw an "m" instead of an "r" and an "n." In other instances you could get a malicious email sent to you from someone you know. If their email account has been hacked, it could be incredibly difficult to identify a phishing email.
Uber Phishing Emails
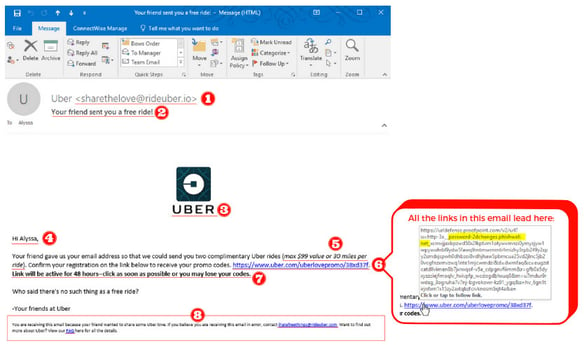
Try this one on your own. Which numbers should tip you off that this is a phishing email?
Read more to see the answers.
The numbers that let you know this is a fraudulent email are: 1, 6 & 8
It's also important to be aware of 2 & 7 because those are both present to try and illicit a rushed decision to click, from the recipient.
Here's a closer look at the role each number was included to perform:
1. The email address is suspicious because it ends in rideuber.io instead of uber.com.
2. Who doesn't love free things? Hackers will use ploys such as winning a prize or money to get you to open the email.
3. The Uber logo has been included to make the email seem legitimate.
4. When cybercriminals send out mass phishing emails, they usually don't address you personally. This way, they can send the email to any number of people. But be sure to stay vigilant to targeted attacks that use your first and last name as well.
5. This cybercriminal took time with the copy to make this email seem legitimate, even going so far as to add a value limit.
6. The web address on the front-end looks like it will take you to Uber.com. But if you hover over the linked text, you can see what url is actually linked to http://password-2dchanges.phishwall.net.
7. They added in that the link will expire within 48 hours to try and get you to click quickly without stopping to think.
8. When hovering over these links, they also appear to lead to password-2dchanges.phishwall.net.
Does your business train its employees on how to avoid phishing emails? Since most malware attacks are initiated via email, it's very important for employees to know what to look for in order to identify a phishing email. If you would like to speak with us about implementing cybersecurity training at your workplace, give us a call at 402.704.8132 or email us at BrewUpInnovation@coretech.us.
Additional Resources:
- How to Catch a Cyber Criminal
- Phishing Baits Hackers Use to Reel You In
- 6 Motivations of Cyber Criminals
